AI-powered reverse engineering assistant that bridges IDA Pro with language models through MCP.
MCP Servers7.4k stars903 forks● PythonMITUpdated today
ClaudeWave Trust Score
100/100
Passed
- ✓Open-source license (MIT)
- ✓Actively maintained (<30d)
- ✓Healthy fork ratio
- ✓Clear description
- ✓Topics declared
- ✓Mature repo (>1y old)
Flags
- !README contains suspicious pattern: eval\s*\(
Last scanned: 4/14/2026
Install in Claude Desktop
Method detected: pip / Python · https
{
"mcpServers": {
"ida-pro-mcp": {
"command": "python",
"args": ["-m", "https"]
}
}
}1. Copy the snippet above.
2. Paste into
~/Library/Application Support/Claude/claude_desktop_config.json (Mac) or %APPDATA%\Claude\claude_desktop_config.json (Windows).3. Replace any
<placeholder> values with your API keys or paths.4. Restart Claude Desktop. The MCP server appears automatically.
💡 Install first: pip install https
Use cases
🧠 AI / ML🎨 Creative🛠️ Dev Tools
About
MCP Servers overview
# IDA Pro MCP
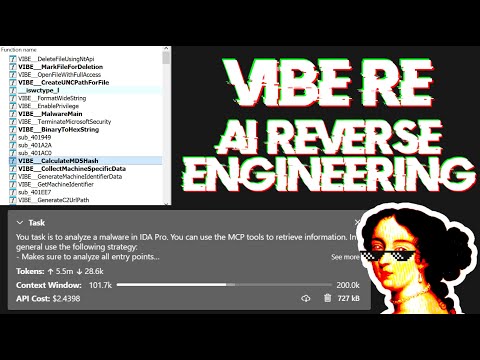
Simple [MCP Server](https://modelcontextprotocol.io/introduction) to allow vibe reversing in IDA Pro.
https://github.com/user-attachments/assets/6ebeaa92-a9db-43fa-b756-eececce2aca0
The binaries and prompt for the video are available in the [mcp-reversing-dataset](https://github.com/mrexodia/mcp-reversing-dataset) repository.
## Prerequisites
- [Python](https://www.python.org/downloads/) (**3.11 or higher**)
- Use `idapyswitch` to switch to the newest Python version
- [IDA Pro](https://hex-rays.com/ida-pro) (8.3 or higher, 9 recommended), **IDA Free is not supported**
- Supported MCP Client (pick one you like)
- [Amazon Q Developer CLI](https://aws.amazon.com/q/developer/)
- [Augment Code](https://www.augmentcode.com/)
- [Claude](https://claude.ai/download)
- [Claude Code](https://www.anthropic.com/code)
- [Cline](https://cline.bot)
- [Codex](https://github.com/openai/codex)
- [Copilot CLI](https://docs.github.com/en/copilot)
- [Crush](https://github.com/charmbracelet/crush)
- [Cursor](https://cursor.com)
- [Gemini CLI](https://google-gemini.github.io/gemini-cli/)
- [Kilo Code](https://www.kilocode.com/)
- [Kiro](https://kiro.dev/)
- [LM Studio](https://lmstudio.ai/)
- [Opencode](https://opencode.ai/)
- [Qodo Gen](https://www.qodo.ai/)
- [Qwen Coder](https://qwenlm.github.io/qwen-code-docs/)
- [Roo Code](https://roocode.com)
- [Trae](https://trae.ai/)
- [VS Code](https://code.visualstudio.com/)
- [VS Code Insiders](https://code.visualstudio.com/insiders)
- [Warp](https://www.warp.dev/)
- [Windsurf](https://windsurf.com)
- [Zed](https://zed.dev/)
- [Other MCP Clients](https://modelcontextprotocol.io/clients#example-clients): Run `ida-pro-mcp --config` to get the JSON config for your client.
## Installation
Install the latest version of the IDA Pro MCP package:
```sh
pip uninstall ida-pro-mcp
pip install https://github.com/mrexodia/ida-pro-mcp/archive/refs/heads/main.zip
```
Configure the MCP servers and install the IDA Plugin:
```
ida-pro-mcp --install
```
**Important**: Make sure you completely restart IDA and your MCP client for the installation to take effect. Some clients (like Claude) run in the background and need to be quit from the tray icon.
https://github.com/user-attachments/assets/65ed3373-a187-4dd5-a807-425dca1d8ee9
_Note_: You need to load a binary in IDA before the plugin menu will show up.
## Prompt Engineering
LLMs are prone to hallucinations and you need to be specific with your prompting. For reverse engineering the conversion between integers and bytes are especially problematic. Below is a minimal example prompt, feel free to start a discussion or open an issue if you have good results with a different prompt:
```md
Your task is to analyze a crackme in IDA Pro. You can use the MCP tools to retrieve information. In general use the following strategy:
- Inspect the decompilation and add comments with your findings
- Rename variables to more sensible names
- Change the variable and argument types if necessary (especially pointer and array types)
- Change function names to be more descriptive
- If more details are necessary, disassemble the function and add comments with your findings
- NEVER convert number bases yourself. Use the `int_convert` MCP tool if needed!
- Do not attempt brute forcing, derive any solutions purely from the disassembly and simple python scripts
- Create a report.md with your findings and steps taken at the end
- When you find a solution, prompt to user for feedback with the password you found
```
This prompt was just the first experiment, please share if you found ways to improve the output!
Another prompt by [@can1357](https://github.com/can1357):
```md
Your task is to create a complete and comprehensive reverse engineering analysis. Reference AGENTS.md to understand the project goals and ensure the analysis serves our purposes.
Use the following systematic methodology:
1. **Decompilation Analysis**
- Thoroughly inspect the decompiler output
- Add detailed comments documenting your findings
- Focus on understanding the actual functionality and purpose of each component (do not rely on old, incorrect comments)
2. **Improve Readability in the Database**
- Rename variables to sensible, descriptive names
- Correct variable and argument types where necessary (especially pointers and array types)
- Update function names to be descriptive of their actual purpose
3. **Deep Dive When Needed**
- If more details are necessary, examine the disassembly and add comments with findings
- Document any low-level behaviors that aren't clear from the decompilation alone
- Use sub-agents to perform detailed analysis
4. **Important Constraints**
- NEVER convert number bases yourself - use the int_convert MCP tool if needed
- Use MCP tools to retrieve information as necessary
- Derive all conclusions from actual analysis, not assumptions
5. **Documentation**
- Produce comprehensive RE/*.md files with your findings
- Document the steps taken and methodology used
- When asked by the user, ensure accuracy over previous analysis file
- Organize findings in a way that serves the project goals outlined in AGENTS.md or CLAUDE.md
```
Live stream discussing prompting and showing some real-world malware analysis:
[](https://www.youtube.com/watch?v=iFxNuk3kxhk)
## Tips for Enhancing LLM Accuracy
Large Language Models (LLMs) are powerful tools, but they can sometimes struggle with complex mathematical calculations or exhibit "hallucinations" (making up facts). Make sure to tell the LLM to use the `int_convert` MCP tool and you might also need [math-mcp](https://github.com/EthanHenrickson/math-mcp) for certain operations.
Another thing to keep in mind is that LLMs will not perform well on obfuscated code. Before trying to use an LLM to solve the problem, take a look around the binary and spend some time (automatically) removing the following things:
- String encryption
- Import hashing
- Control flow flattening
- Code encryption
- Anti-decompilation tricks
You should also use a tool like Lumina or FLIRT to try and resolve all the open source library code and the C++ STL, this will further improve the accuracy.
## SSE Transport & Headless MCP
You can run an SSE server to connect to the user interface like this:
```sh
uv run ida-pro-mcp --transport http://127.0.0.1:8744/sse
```
After installing [`idalib`](https://docs.hex-rays.com/user-guide/idalib) you can also run a headless SSE server:
```sh
uv run idalib-mcp --host 127.0.0.1 --port 8745 path/to/executable
```
_Note_: The `idalib` feature was contributed by [Willi Ballenthin](https://github.com/williballenthin).
## Headless idalib Session Model
Use `--isolated-contexts` to enable strict per-transport isolation:
```sh
uv run idalib-mcp --isolated-contexts --host 127.0.0.1 --port 8745 path/to/executable
```
### Why use `--isolated-contexts`?
Use it when multiple agents connect to the same `idalib-mcp` server and you want deterministic context isolation:
- Prevent one agent from changing another agent's active session accidentally.
- Run concurrent analyses safely (for example agent A on binary X and agent B on binary Y).
- Still allow intentional collaboration by binding multiple agents to the same open session ID.
- Improve reproducibility because each agent's context binding is explicit.
When `--isolated-contexts` is enabled:
- Each transport context has its own binding (`Mcp-Session-Id` for `/mcp`, `session` for `/sse`, `stdio:default` for stdio).
- Unbound contexts fail fast for IDB-dependent tools/resources.
- `idalib_switch(session_id)` and `idalib_open(...)` bind the caller context only.
### Streamable HTTP behavior
With `--isolated-contexts`, strict Streamable HTTP session semantics are enabled, including `Mcp-Session-Id` validation.
### Context tools
- `idalib_open(input_path, ...)`: Open binary and bind it to the active context policy.
- `idalib_switch(session_id)`: Rebind the active context policy to an existing session.
- `idalib_current()`: Return the session bound to the active context policy.
- `idalib_unbind()`: Remove the active context binding.
- `idalib_list()`: Includes `is_active`, `is_current_context`, and `bound_contexts`.
## MCP Resources
**Resources** represent browsable state (read-only data) following MCP's philosophy.
**Core IDB State:**
- `ida://idb/metadata` - IDB file info (path, arch, base, size, hashes)
- `ida://idb/segments` - Memory segments with permissions
- `ida://idb/entrypoints` - Entry points (main, TLS callbacks, etc.)
**UI State:**
- `ida://cursor` - Current cursor position and function
- `ida://selection` - Current selection range
**Type Information:**
- `ida://types` - All local types
- `ida://structs` - All structures/unions
- `ida://struct/{name}` - Structure definition with fields
**Lookups:**
- `ida://import/{name}` - Import details by name
- `ida://export/{name}` - Export details by name
- `ida://xrefs/from/{addr}` - Cross-references from address
## Core Functions
- `lookup_funcs(queries)`: Get function(s) by address or name (auto-detects, accepts list or comma-separated string).
- `int_convert(inputs)`: Convert numbers to different formats (decimal, hex, bytes, ASCII, binary).
- `list_funcs(queries)`: List functions (paginated, filtered).
- `list_globals(queries)`: List global variables (paginated, filtered).
- `imports(offset, count)`: List all imported symbols with module names (paginated).
- `decompile(addr)`: Decompile function at the given address.
- `disasm(addr)`: Disassemble function with full details (arguments, stack frame, etc).
- `xrefs_to(addrs)`: Get all cross-references to address(es).
- `xrefs_to_field(queries)`: Get cross-references to specific struct field(s).
- `callees(addrs)`: Get functions called by function(s) at address(es).
## Modification Operations
- `set_comTopics
aiaiagentbinary-analysisida-pluginida-promcpmcp-servermodelcontextprotocolreverse-engineering
Related
More MCP Servers
n8n-io
n8n
✓95
Fair-code workflow automation platform with native AI capabilities. Combine visual building with custom code, self-host or cloud, 400+ integrations.
184k56.8kTypeScript· today
MCP Serversaiapis
open-webui
open-webui
✓89
User-friendly AI Interface (Supports Ollama, OpenAI API, ...)
131.8k18.7kPython· today
MCP Serversaillm
google-gemini
gemini-cli
✓98
An open-source AI agent that brings the power of Gemini directly into your terminal.
101.2k13.1kTypeScript· today
MCP Serversaiai-agents
punkpeye
awesome-mcp-servers
✓87
A collection of MCP servers.
84.8k9.1k· today
MCP Serversaimcp
netdata
netdata
✓97
The fastest path to AI-powered full stack observability, even for lean teams.
78.4k6.4kC· today
MCP Serversaialerting
Mintplex-Labs
anything-llm
✓93
The all-in-one AI productivity accelerator. On device and privacy first with no annoying setup or configuration.
58.3k6.3kJavaScript· today
MCP Serversai-agentscustom-ai-agents